How to give great employee performance reviews

A Dropbox Sign blog about
All articles
Sign contracts 80% faster
Go paperless with Dropbox Sign.
Try Dropbox Sign
The foolproof guide to creating the perfect hiring sequence
Build a simple, streamlined, easy to follow and execute hiring process so that positive candidate experience becomes standard.
Download


Sales tips

5
minute read
How to turbo-charge your CRM with eSignatures (and why it’s the key to growth)

Human resources advice

5
minute read
Slow hiring process? Here are 5 ways to optimize your time-to-hire
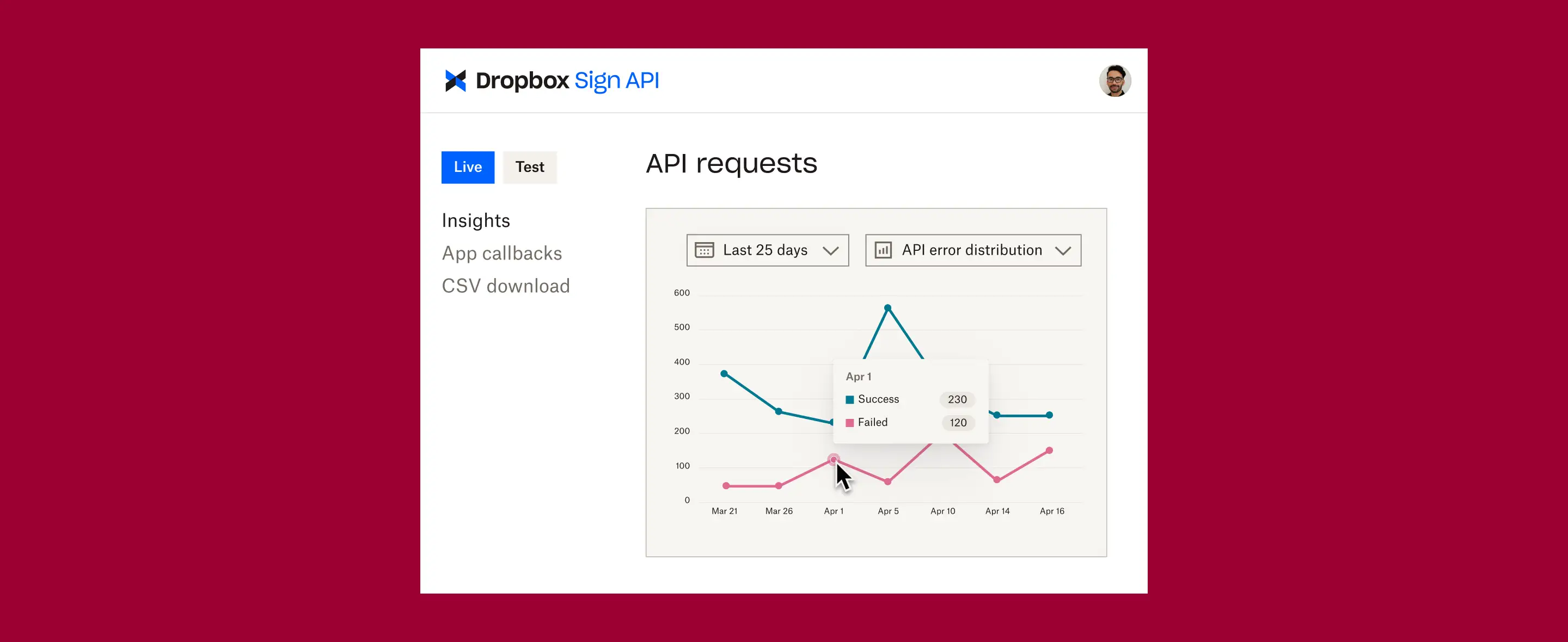
Dropbox Sign integrations
Ready to experience our new and improved Dropbox Sign for HubSpot integration?
We’re offering new Dropbox Sign users 50% off the first year!
Start your free trial


































































![How To Boost Buyer's Confidence [Updated 2023] editorial illustration](https://assets-global.website-files.com/6446df33610093270e7fb677/645a79cf551d724a508f6ce3_6449bddbf539fc2c4cbafc7f_uc.webp)
![How To Boost Buyer's Confidence [Updated 2023] editorial illustration](https://assets-global.website-files.com/6446df33610093270e7fb677/645a79cf551d720f3c8f6ce4_6449bddbf539fc49dabafc81_uc.webp)





















.webp)